The idea of pass phrases in favour of passwords has intrigued me ever since I read the iconic XKCD, Password Strength comic.
Munroe's argument goes that conventional wisdom about secure passwords is stupid and misguided. Experts tell us to use a password that is at least 8 characters long - exactly a character longer than most humans can comfortably store in short term memory - contains mixed case letters and numbers.
Special characters are a good idea as well, but almost nobody uses them because more often than not services reject them on grounds that ... I don't know, I guess their databases don't support fancy passwords or something. Don't even get me on services with so many password rules the possibility space collapses into, like, 10.
These passwords are impossible to remember. Meaning people use simple passwords instead.
You're supposed to change your password every few months as well! People don't, because they're too hard to remember.
You should use a different password everywhere! People don't, because they're too hard to remember.
Passwords suck
To make matters worse, "secure" passwords aren't secure at all. An 8 character password considering common alphanumeric characters people use most often gives you 60^8 combinations. At 1000 guesses per second this is guessable in about 5000 years.
Okay, that's impractical. You're better off using a different vector of attack ... like a good wrench to the wrist. Or those stupid security questions.
But passwords aren't random sequences of letters! Remember, people can't memorise those. Most often they use a common word and capitalize the first letter, then add a few numbers at the end. Or possibly some numbers at the start.
There are just 15,222 6 letter words in the English language, giving enough room to add two numbers. Accounting for capitalizing the first letter that gives us 25^2+15222+10^2 combinations. Guessable in about 15 seconds.
Oops.
Including common substitions - 1337 sp34k - gives us a few more combinations and the usual password is guessable in about three days. And that's with a very secure looking password that is almost impossible to remember!
Sure, we cheated a bit by using a dictionary attack, but hey, anything goes! I'm sure real attackers have even more tricks up their sleeves.
Pass phrases win

Take pass phrases on the other hand.
Using a combination of three or four common words is something you do every day. Your brain is hard wired to be great at memorising this stuff ... remember all those cool lines you're still referencing from movies made 40 years ago!
Three is the number you shall count! The number of the counting shall be three!
Khm, yes.
The great thing about pass phrases is that they are usually long. Very long.
An average english word is about 7 characters long, three words create a password with 21 characters. With a dispersion of 2 characters per word, your password will likely be 15 to 21 letters, adding spaces and you're at 17 to 23.
Now, assuming you're using nothing but lower case letters and spaces that still gives 26^17 combinations. Guessable in about 3 tera years. That's 3 and 13 zeros.
Nobody's guessing that via a character by character attack.
Let's look at a dictionary attack then, that saved us before, maybe it will help now.
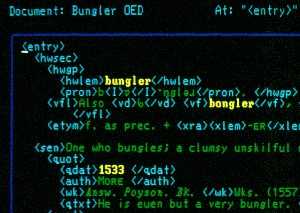
There are 171,476 words in the Oxford English Dictionary. Using just 3 words, any words, gives you 3^171476 combinations. In other words, a dictionary attack at 1000 guesses per second would take so many years the number's got 81,804 digits.
Eighty one thousand digits.
That's longer than the expected death of the universe isn't it?
Sure, not all combinations of words make sense, some words are more common than others. The vocabulary of an average college grad measures at about 17,000 words. That still gives you 3^17000 combinations, or an 8100 digit number of years to guess.
Without funny symbols. Without numbers. Just simple lowercase words.
I'm already switching all my passwords to pass phrases. You should too!
Continue reading about In praise of the pass phrase
Semantically similar articles hand-picked by GPT-4
- Week 12: practical cold boot attacks that will make cryptonerds shit their pants
- Code completion is bad mmkay
- Slovenia Php Conference 2009 (live blogging)
- I learned two things today 5.8.
- A tale about always-on DRM and web security
Learned something new?
Read more Software Engineering Lessons from Production
I write articles with real insight into the career and skills of a modern software engineer. "Raw and honest from the heart!" as one reader described them. Fueled by lessons learned over 20 years of building production code for side-projects, small businesses, and hyper growth startups. Both successful and not.
Subscribe below 👇
Software Engineering Lessons from Production
Join Swizec's Newsletter and get insightful emails 💌 on mindsets, tactics, and technical skills for your career. Real lessons from building production software. No bullshit.
"Man, love your simple writing! Yours is the only newsletter I open and only blog that I give a fuck to read & scroll till the end. And wow always take away lessons with me. Inspiring! And very relatable. 👌"
Have a burning question that you think I can answer? Hit me up on twitter and I'll do my best.
Who am I and who do I help? I'm Swizec Teller and I turn coders into engineers with "Raw and honest from the heart!" writing. No bullshit. Real insights into the career and skills of a modern software engineer.
Want to become a true senior engineer? Take ownership, have autonomy, and be a force multiplier on your team. The Senior Engineer Mindset ebook can help 👉 swizec.com/senior-mindset. These are the shifts in mindset that unlocked my career.
Curious about Serverless and the modern backend? Check out Serverless Handbook, for frontend engineers 👉 ServerlessHandbook.dev
Want to Stop copy pasting D3 examples and create data visualizations of your own? Learn how to build scalable dataviz React components your whole team can understand with React for Data Visualization
Want to get my best emails on JavaScript, React, Serverless, Fullstack Web, or Indie Hacking? Check out swizec.com/collections
Did someone amazing share this letter with you? Wonderful! You can sign up for my weekly letters for software engineers on their path to greatness, here: swizec.com/blog
Want to brush up on your modern JavaScript syntax? Check out my interactive cheatsheet: es6cheatsheet.com
By the way, just in case no one has told you it yet today: I love and appreciate you for who you are ❤️